In today's digital landscape, safeguarding your valuable data and systems is paramount. Businesses across industries are increasingly vulnerable to sophisticated cyber threats. To effectively mitigate these risks and fortify your defenses, partnering with a reputable Information Security Consulting can be invaluable.
These experts possess the in-depth knowledge, skills, and experience to conduct thorough Vulnerability Analyses, identify potential weaknesses, and recommend tailored Mitigation Techniques. They can help you implement robust security protocols, Strengthen Data Protection , and provide ongoing Monitoring and Maintenance to ensure your digital assets remain secure.
By leveraging the expertise of an Information Security Consultant, you can significantly reduce your exposure to cyber threats, protect your sensitive information, and maintain a secure and resilient digital environment.
Charting the Complex Landscape of Data Protection
In today's online age, data has become an invaluable resource. However, its criticality necessitates robust measures to ensure its security. Organizations face a challenging landscape of regulations aimed at preserving personal information. Adherence with these standards is crucial to avoid consequences.
- Integrating strong data protection measures
- Performing regular audits
- Educating employees on data security best practices
By implementing a integrated approach to data protection, businesses can effectively address the risks associated with data compromises.
A Preemptive Approach to Cyber Security
In today's rapidly evolving threat landscape, organizations must shift their focus from reactive responses to proactive threat mitigation strategies. This comprehensive approach involves implementing a multi-layered security framework that anticipates potential vulnerabilities and implements measures to deter attacks before they can occur. By adopting cutting-edge technologies, conducting thorough risk assessments, and fostering a culture of security awareness, organizations can significantly reduce get more info their exposure to cyber threats and protect their valuable assets.
- Essential elements of a proactive threat mitigation strategy include:
- Layered defenses to thwart unauthorized access.
- Security education initiatives to mitigate human error as a risk factor.
- Regular vulnerability assessments and penetration testing to identify weaknesses and address them promptly.
Cybersecurity Strategy and Implementation for Businesses of All Sizes
In today's virtual landscape, a robust cybersecurity strategy is paramount for businesses of all dimensions. A well-defined strategy outlines the measures necessary to protect sensitive data and networks from ever-evolving threats. Whether you're a small enterprise, implementing a comprehensive cybersecurity plan can mitigate risks and safeguard your organization's value.
- Start with a thorough risk assessment to identify potential weaknesses in your current security posture.
- Implement multi-factor authentication (MFA) for all user accounts to prevent unauthorized access.
- Educate employees about cybersecurity best practices and the importance of awareness.
- Regularly update software and hardware to patch vulnerabilities and protect against known threats.
- Consider implementing a security information and event management (SIEM) system to monitor and analyze security logs in real time.
By taking proactive steps to strengthen your cybersecurity defenses, you can create a more secure environment for your business and its valuable data. Remember, a strong cybersecurity position is an ongoing process that requires continuous assessment and adaptation.
Enhancing Your Risk Posture with Expert Information Security Guidance
In today's volatile digital/cyber/online landscape, organizations face a multitude of threats. To effectively mitigate these risks and strengthen your overall security posture, expert information security guidance is crucial. A seasoned security consultant can analyze your current infrastructure/systems/environment, identify weaknesses, and develop a tailored strategy to bolster your defenses.
This comprehensive approach often includes areas such as:
- Implementing robust security controls
- Performing regular penetration testing and vulnerability assessments
- Developing comprehensive incident response plans
- Educating employees on best practices for information security
By harnessing expert information security guidance, your organization can strategically elevate its risk posture and achieve a more secure future.
Securing Your Future: Tailored Information Security Solutions
In today's rapidly evolving digital landscape, information/cyber/digital security has become paramount. Businesses of all dimensions face an ever-increasing threat from sophisticated attackers. To effectively defend against these threats, it is essential to implement comprehensive security measures that are tailored to your unique needs and situation. A proactive approach to information security involves analyzing your existing infrastructure, identifying potential vulnerabilities, and developing a multi-faceted security strategy that addresses your specific priorities.
Such means selecting the right technologies and implementing best practices to safeguard your valuable data. Additionally, it requires ongoing analysis and adjustment to stay ahead of emerging threats. By investing in dedicated security professionals, you can gain the expertise necessary to enhance your defenses and confidently navigate the complexities of the digital world.
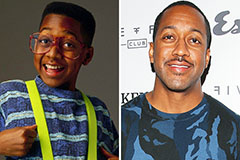 Jaleel White Then & Now!
Jaleel White Then & Now! Neve Campbell Then & Now!
Neve Campbell Then & Now! Barret Oliver Then & Now!
Barret Oliver Then & Now! Samantha Fox Then & Now!
Samantha Fox Then & Now! Robin McGraw Then & Now!
Robin McGraw Then & Now!